Data Breaches: Understanding Risks, Response & Prevention

A data breach is any security incident in which unauthorized parties access sensitive or confidential information. This guide explains what a data breach is, how breaches happen, their impact on organizations and individuals, and how to prevent and respond to them. It is intended for business leaders, IT professionals, and anyone concerned about data security, as understanding data breaches is critical to protecting sensitive information and maintaining trust. The scope of this guide includes the definition of data breaches, common causes and attack vectors, the financial, legal, and reputational impacts, as well as best practices for prevention and effective response. Understanding data breaches matters because the risks are significant: organizations face not only financial losses but also legal liabilities and damage to their reputation if sensitive data is compromised.
The financial and operational impact of a data breach is enormous. The global average cost of a data breach is approximately $4.44 million, while the average cost of a data breach in the United States is USD 10.22 million. The average breach takes over five months to identify and contain. The healthcare industry faces even higher costs, with the average healthcare data breach costing $7.42 million in 2025. In addition to financial loss, breaches can disrupt business operations, cause reputational damage, and lead to regulatory penalties.
Understanding how data breaches happen and responding quickly when a data breach incident occurs is essential for protecting affected individuals and minimizing long-term damage to organizations. The 2007 data breach of TJX Corporation compromised the data of approximately 94 million customers and resulted in over USD 256 million in losses.
Understanding a Data Breach and Why Data Breaches Happen
A data breach is any security incident in which unauthorized parties gain access to sensitive information, corporate data, or private data stored in a computer system or network. These breaches can result from intentional cyber attacks or accidental exposure caused by human error.
Cyberattacks often follow a basic pattern: attackers conduct research on their targets, identify vulnerabilities, and then execute their plan in a structured and methodical way to maximize their chances of success.
How Data Breaches Happen: Common Attack Vectors
Many breaches occur when cyber criminals exploit weak passwords, stolen credentials, vulnerable operating systems, or poorly secured cloud environments. Attackers may also use phishing attacks, social engineering, or malicious software to compromise login credentials and infiltrate a target’s network. Phishing is the most common type of social engineering attack and accounts for a significant percentage of data breaches.
Social Engineering and Phishing Attacks
Phishing is the most common type of social engineering attack and accounts for a significant percentage of data breaches. Attackers use deceptive emails, messages, or phone calls to trick individuals into revealing sensitive information or clicking malicious links.

Stolen Credentials and Weak Passwords
Many breaches occur when cyber criminals exploit weak passwords or use stolen credentials to gain unauthorized access to systems and data.
Malicious Insider Threats
Breaches may also be caused by internal threats. A malicious insider with legitimate access privileges may intentionally leak or sell compromised information with the goal of causing harm to the organization or individuals. Malicious insiders, including angry or laid-off employees, can cause data breaches by stealing or leaking information. Insiders or external attackers may steal data for financial gain, espionage, or sabotage. In other cases, innocent mistakes — such as an employee emailing sensitive information to the wrong recipient — can lead to data leaks that expose confidential data.
Technical Exploits
Attackers can exploit weaknesses in websites, operating systems, and software to carry out data breaches. Common technical exploits include:
- Malware: Malicious software designed to intercept data from a victim’s device or network.
- SQL Injection: Attackers exploit vulnerabilities in website databases to access or manipulate sensitive data.
- Supply Chain Attacks: Hackers exploit vulnerabilities in the networks of a company's service providers to steal data.
Stolen or compromised credentials account for a notable percentage of data breaches and can take a long time to identify.
Human error accounts for a significant portion of data breaches, often due to negligence or lack of awareness. Employees are often the weakest link in cybersecurity, making comprehensive awareness and training essential to prevent breaches.
The consequences can be severe. Malicious actors can use stolen account information, customer information, or bank accounts to commit identity theft, make fraudulent purchases, or sell stolen information on the dark web.
Understanding these attack vectors is crucial, but knowing how to respond when a breach occurs is equally important.
Immediate Response to a Data Breach Incident
When a data breach incident occurs, organizations must act quickly to secure their systems and prevent further damage. The first step is to contain the breach by identifying the compromised systems and stopping unauthorized access.
Organizations should move quickly to secure systems and fix vulnerabilities that may have caused the breach. This may include disabling compromised user accounts, patching software vulnerabilities, removing malicious software, and strengthening access controls to prevent attackers from regaining access.
It is critical to assemble a team of experts that includes security teams, incident response specialists, IT administrators, and legal counsel to conduct a comprehensive breach response. This team should analyze the attack, determine how the breach occurred, and identify what data or systems were compromised.
Investigators should carefully document their findings and preserve evidence during the investigation process. Destroying logs or system evidence could interfere with law enforcement investigations and make it harder to understand how attackers gained access.
Organizations should also implement continuous monitoring to detect additional malicious activity and ensure that attackers have been completely removed from the environment.
While response is critical, prevention remains the best defense. The next section explores key strategies for reducing the risk of a data breach.
Complying with Data Breach Notification Laws
After identifying the scope of the breach, organizations must comply with data breach notification laws that require affected businesses to notify regulators and individuals whose data was compromised. Each state has enacted its own state law regarding breach notification requirements, so organizations must check applicable state laws to ensure compliance.
In the United States, all states, the District of Columbia, Puerto Rico, and the Virgin Islands have enacted laws requiring notification of security breaches involving personal information. These laws typically require organizations to notify individuals when their personally identifiable information (PII) has been exposed. PII refers to sensitive or confidential information that can be used to identify an individual.
Organizations that process healthcare data must follow additional regulations. Under HIPAA, organizations must notify the Department of Health and Human Services, affected individuals, and sometimes the media if protected health data has been compromised.
International regulations also apply in many cases. The General Data Protection Regulation (GDPR) requires companies doing business with EU citizens to report certain breaches to authorities within 72 hours.
Organizations should consult with law enforcement and legal experts before issuing breach notifications to ensure that communications do not interfere with ongoing investigations.
Failure to comply with data breach notification laws can result in severe penalties, legal action, and regulatory fines. It is crucial to follow all data breach notification laws to avoid hefty fines.
Additionally, the US Cyber Incident Reporting for Critical Infrastructure Act of 2022 (CIRCIA) requires organizations in national security, finance, and other designated industries to report cybersecurity incidents affecting personal data or business operations to the Department of Homeland Security within 72 hours.
Transitioning from legal compliance, organizations must also focus on clear and timely communication with those affected by a breach.
Communicating with Affected Individuals
Once the breach is confirmed, organizations must notify affected individuals and provide guidance on how they can protect themselves from potential misuse of their data.
Companies should create a comprehensive communications plan to inform all affected audiences. This may include customers, employees, business partners, and government agencies that regulate data protection.
Organizations should notify individuals quickly so they can take steps to protect themselves from identity theft or financial fraud. In many cases, companies offer free credit monitoring services to individuals whose financial information may have been exposed.
Notifications should explain what information was compromised, how the breach occurred, and what actions the organization is taking to improve data security. Individuals should also be encouraged to monitor their accounts for suspicious activity and report misuse of their information to the Federal Trade Commission (FTC).
With communication underway, organizations must also assess the broader financial and business impacts of the breach.
The Financial and Business Impact of Data Breaches
A major data breach can have significant financial consequences for organizations. In addition to the costs of investigating and containing the breach, companies may face legal settlements, regulatory fines, and lost business.
Post-breach expenses can include legal fees, settlements, and regulatory penalties that average $1.20 million per incident. Organizations also spend approximately $390,000 on notification costs, including contacting affected individuals and regulatory authorities.
The damage to reputation and customer trust can be even more costly. Many companies experience lost business, reduced customer confidence, and long-term reputational harm after a major breach.
Some of the most well-known breaches in history demonstrate the scale of these incidents. The Yahoo data breach in 2013 affected 3 billion user accounts, making it one of the largest breaches ever recorded. The Equifax breach in 2017 exposed the personal data of over 143 million Americans after attackers exploited an unpatched vulnerability.
More recently, attackers stole data from 6.9 million 23andMe users in 2023 through a credential stuffing attack, demonstrating how stolen login credentials remain one of the most common entry points for cyber attacks.
Understanding the impact of breaches highlights the importance of robust prevention strategies, which are explored in the next section.
Data Breach Prevention and Strengthening Data Security
While responding effectively to a breach is critical, organizations must also prioritize data breach prevention to reduce the likelihood of future incidents.
Employee Training
Organizations should implement employee training programs to educate staff about phishing scams, malicious links, and social engineering attacks. Because human error remains one of the weakest links in cybersecurity, regular training can significantly reduce the risk of breaches caused by employee mistakes. Employees should also be made aware of the risks of downloading sensitive data to unsecured devices, as attackers can exploit poor device security. User education is essential to mitigate risks associated with unsecured devices.
Access Management
Organizations should implement strong access management policies that limit employee access privileges to only the data required for their roles. Adopting the principle of least privilege can significantly reduce the risk of internal threats and accidental exposure of sensitive information.
Using multi factor authentication can protect employee accounts from unauthorized access, especially when attackers attempt to exploit stolen credentials. Using strong passwords and enabling two-factor authentication can protect employee accounts from unauthorized access. Security experts increasingly recommend phishing-resistant MFA using hardware security keys rather than SMS-based authentication.
Attackers can exploit text messages, along with emails and social media, to deceive users into revealing sensitive credentials or downloading malware, thereby facilitating data breaches.
Encryption
Encrypting sensitive data, monitoring network activity, and adopting a zero trust security model can further strengthen an organization’s security posture and protect critical assets.
Incident Response Planning
Regular vulnerability assessments and timely patching of systems are also essential. Cybercriminals frequently exploit weaknesses in websites, operating systems, and software to carry out attacks. Identifying and fixing these vulnerabilities quickly helps prevent attackers from gaining access to sensitive systems.
Zero-Trust Model
Data exposure can occur when unprotected server databases contain user IDs linked to personal data, increasing the risk of data breaches. It is important to protect user IDs in server databases to prevent unauthorized access to sensitive information.
Transitioning from prevention strategies, organizations must also focus on empowering their workforce through education and training to ensure preparedness for evolving threats.
Employee Education and Training for Data Breach Preparedness
The cybersecurity landscape continues to evolve at breakneck speed, but one vulnerability remains stubbornly persistent: the human element. Employee education and training form the cornerstone of effective data breach prevention strategies, serving as the critical first barrier between threat actors and sensitive organizational assets. While sophisticated security tools grab headlines, industry data consistently shows that human error and inadequate security awareness drive a substantial percentage of successful breach attempts. Organizations that invest strategically in comprehensive training programs don't just reduce risk — they transform their workforce from potential liability into active defense participants, safeguarding everything from personally identifiable information to critical financial data.
Why Employee Training Matters
Modern threat landscapes demand training programs that address real-world attack vectors with precision and clarity. Effective security education must cover social engineering recognition, particularly the evolving sophistication of phishing campaigns that bypass traditional email filters.
Key Training Topics
Password hygiene remains fundamental — not just creating strong credentials, but understanding why credential reuse across systems creates cascading vulnerabilities. Multi-factor authentication implementation requires more than mandate; employees need to understand the security rationale behind additional verification steps. Beyond basic protocols, staff must grasp proper handling procedures for sensitive information categories, whether processing customer records, managing confidential business intelligence, or protecting high-value intellectual property. Regular training cycles, supplemented by realistic phishing simulations, help maintain security awareness as an active mindset rather than passive compliance.
Building a Security-Aware Culture
Legal compliance and incident response capabilities hinge on employee familiarity with notification requirements and internal escalation procedures. When security incidents occur — and industry statistics suggest they're increasingly inevitable rather than possible — response speed often determines breach scope and regulatory consequences. Staff training must encompass not only technical response protocols but also legal obligations under relevant data protection frameworks. Quick, appropriate incident reporting can mean the difference between contained exposure and widespread compromise, directly impacting both immediate damage control and long-term compliance standing.
Building genuine security culture requires moving beyond checkbox training toward sustained engagement with protection principles. Organizations that succeed in this transformation empower their workforce to think proactively about threat identification and mitigation, creating distributed defense capabilities that extend far beyond traditional perimeter security. This cultural shift delivers compound benefits: reduced incident probability, faster threat detection when problems arise, and more effective organizational response when breaches occur. In today's threat environment, employee security awareness isn't just good practice — it's operational necessity.
With a well-trained workforce, organizations can further strengthen their defenses by implementing robust identity and access management solutions.
Identity and Access Management Solutions
Identity and access management has emerged as a cornerstone of modern enterprise security architecture, serving as the primary defense against data breaches that continue to plague organizations across industries. These frameworks act as digital gatekeepers, controlling who gains entry to crown jewel assets — customer databases, proprietary research, and financial systems that attackers prize most. Without proper IAM controls, organizations essentially leave their front doors unlocked in an environment where cybercriminals are constantly probing for weaknesses.
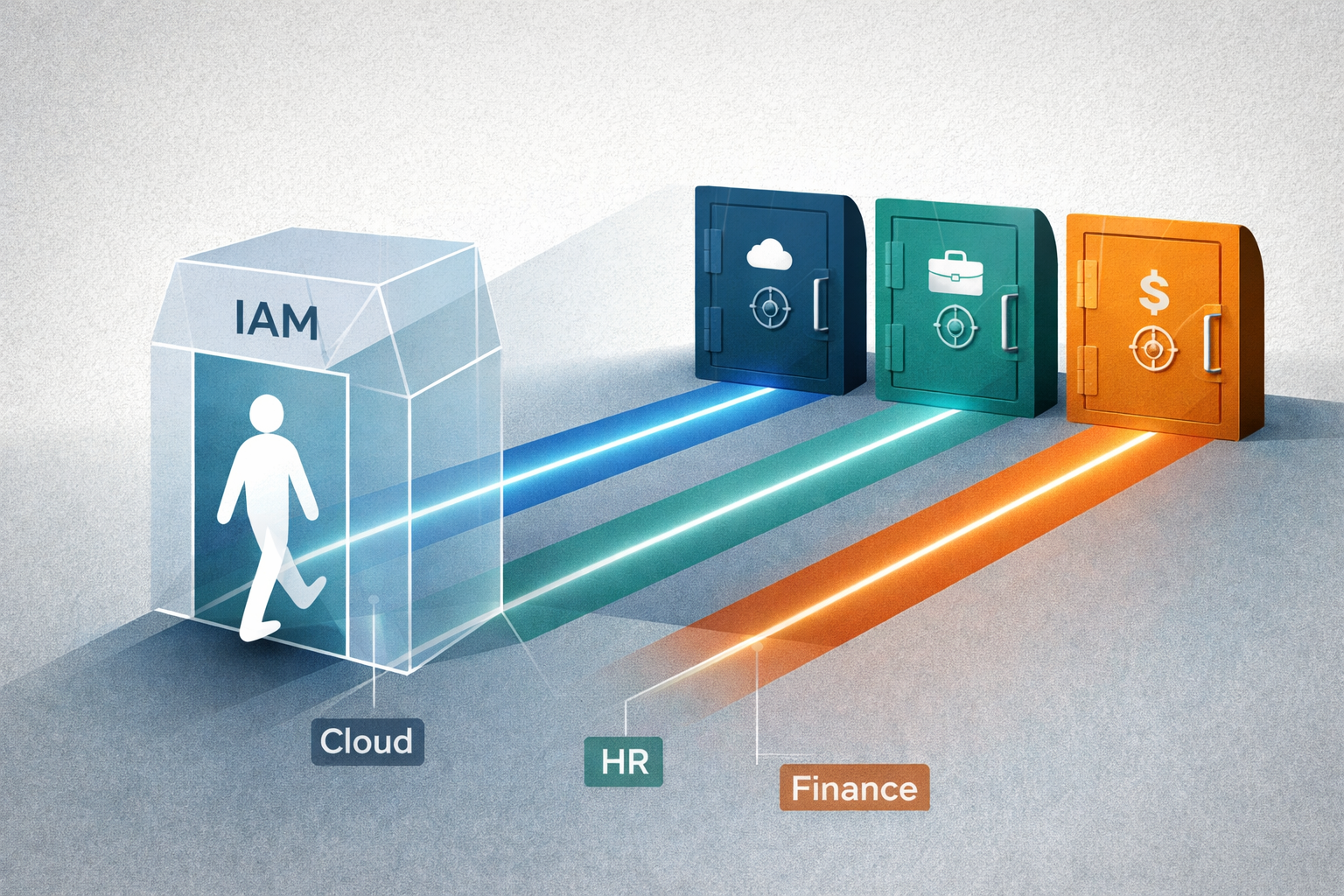
The most effective IAM deployments center on two fundamental security principles that have proven their worth in countless breach scenarios. Multi-factor authentication transforms the traditional password from a single point of failure into just one component of a layered defense strategy. Meanwhile, role-based access control ensures employees can only reach the systems and data directly relevant to their job functions — a critical safeguard that prevents lateral movement during successful intrusions. Organizations implementing the principle of least privilege create significant hurdles for both external attackers operating with compromised credentials and malicious insiders looking to abuse their access.
Modern IAM platforms excel at threat detection through continuous monitoring capabilities that can spot anomalous behavior patterns in real-time. These systems flag unusual login times, geographic inconsistencies, and access attempts that deviate from established user behaviors. Security teams gain valuable visibility into potential insider threats and account compromises before attackers can establish persistent access or begin data exfiltration operations. This proactive approach has become essential as threat actors increasingly rely on stolen credentials rather than malware to infiltrate target networks.
Regulatory compliance has transformed from a checkbox exercise into a business necessity, with IAM serving as the foundation for meeting evolving data protection requirements. Healthcare organizations, financial institutions, and companies handling personal information must demonstrate robust access controls and maintain comprehensive audit trails to satisfy regulators. Strong authentication measures and detailed logging capabilities help organizations avoid the devastating financial penalties and reputation damage that follow major data breaches. These compliance benefits extend beyond avoiding fines to building customer trust and competitive advantage in security-conscious markets.
Implementing comprehensive IAM solutions represents a strategic investment in organizational resilience as cyber threats continue to evolve in sophistication and scale. The current threat landscape demands more than traditional perimeter defenses — it requires granular control over user access, continuous monitoring of authentication events, and rapid response capabilities when security incidents occur. Organizations that prioritize IAM implementation position themselves to weather the inevitable security challenges while maintaining operational efficiency and regulatory compliance.
With IAM solutions in place, organizations should also develop a comprehensive incident response strategy to ensure readiness for any security incident.
Building a Strong Incident Response Strategy
One of the most effective ways organizations can prepare for a breach is by developing and testing a well-defined incident response plan.
A strong incident response plan should outline how security teams detect and respond to cyber incidents, communicate with stakeholders, and coordinate with law enforcement when necessary.
Organizations should conduct regular risk assessments to identify critical systems and high-value data that require additional protection. Threat intelligence can also help organizations anticipate emerging threats and adapt their security strategies accordingly.
Monitoring, reviewing, and improving security measures continuously allows organizations to stay ahead of evolving cyber threats.
By combining proactive security measures with effective breach response strategies, organizations can reduce the likelihood of major security incidents and minimize the impact when breaches occur.
Conclusion
In conclusion, data breaches pose an escalating threat that no organization can afford to ignore. The stakes continue rising as attackers grow more sophisticated, leaving companies facing potential financial devastation, irreparable brand damage, and serious consequences for customers whose information falls into the wrong hands. Building effective defenses requires more than a single security tool — it demands a layered strategy that weaves together workforce education, robust identity controls, and continuous security monitoring.
When breaches do occur, response speed makes all the difference. Organizations need incident response playbooks ready to execute immediately, ensuring they meet regulatory notification deadlines and communicate transparently with affected users. The most successful defense strategies focus heavily on the human element — teaching staff to spot phishing attempts and social engineering tactics while implementing strict access controls that limit what each user can reach within corporate systems.
Security teams that stay ahead of emerging attack methods and implement proven response measures like credit monitoring services for victims can significantly reduce breach impact. Companies that excel at protecting sensitive customer data and financial records through strong access management create a competitive advantage while building customer trust.
Ultimately, the organizations that thrive in today's threat landscape are those that treat security as an ongoing commitment rather than a one-time project. Regular security audits, updated policies that reflect current regulations, and a company-wide culture where everyone understands their role in protecting data — these practices separate resilient organizations from those that become tomorrow's breach headlines.
FAQ
What is a data breach?
A data breach is a security incident in which unauthorized individuals gain access to sensitive information such as personal data, financial records, or login credentials.
What information is typically exposed in a data breach?
Data breaches often expose personally identifiable information such as social security numbers, bank account numbers, credit card details, phone numbers, and login credentials. In breaches involving government agencies, sensitive information such as military operations and political dealings may also be exposed.
How should organizations respond to a data breach?
Organizations should secure affected systems, investigate the breach, notify regulators and affected individuals, and strengthen security controls to prevent future incidents.
What laws require companies to report data breaches?
Many jurisdictions have data breach notification laws requiring companies to notify individuals when their personal data is exposed. Regulations such as GDPR and HIPAA also require breach reporting.
How can organizations prevent data breaches?
Organizations can reduce the risk of data breaches by implementing multi-factor authentication, employee security training, strong access management policies, encryption, and continuous monitoring.
Why are data breaches so damaging for organizations?
Data breaches can result in financial losses, regulatory fines, reputational damage, and loss of customer trust, making them one of the most serious cybersecurity risks businesses face. In some cases, state sponsored hackers are involved, causing particularly damaging breaches by targeting sensitive information for espionage or strategic advantage.
Famous Real-World Data Breaches
| Incident | Year | Impact | Key Details |
|---|---|---|---|
| Yahoo | 2013 | 3 billion user accounts | Largest breach ever recorded; attackers accessed user account information. |
| Equifax | 2017 | 143 million Americans | Attackers exploited unpatched vulnerability; exposed PII and credit data. |
| TJX Corporation | 2007 | 94 million customers | Data theft resulted in over $256 million in losses. |
| 23andMe | 2023 | 6.9 million users | Credential stuffing attack; attackers used stolen login credentials. |




