Advanced Persistent Threats (APT) Explained: How They Work

An advanced persistent threat (APT) represents one of the most dangerous categories of modern cyber threats. These attacks are considered sophisticated threats due to their complexity and the advanced tactics used by attackers. Unlike opportunistic attacks, an advanced persistent threat attack is carefully planned, highly targeted, and executed over an extended period with the goal of infiltrating a network, maintaining access, and extracting sensitive data without detection. Large organizations are frequent targets of APTs due to their expansive attack surfaces and the valuable data they possess.
This guide is intended for IT professionals, security teams, and business leaders seeking to understand and defend against APTs. Understanding APTs is essential for organizations that manage sensitive data or critical infrastructure, as these threats can cause significant long-term damage.
The term advanced persistent threat originated from the United States Air Force in 2006, and it has since become synonymous with cyber espionage, stealth operations, and nation-state cyber campaigns. Today, APT attackers are often backed by significant resources, allowing them to deploy advanced tools — including both offensive and defensive security tools — exploit vulnerabilities, and continuously adapt to defenses inside an organization’s network. The deployment of advanced security tools is crucial for protecting an organization’s network against these evolving threats. Continuous monitoring is also essential for proactive threat detection and response against APTs.
What Is an Advanced Persistent Threat (APT)?
An advanced persistent threat (APT) is a stealthy threat typically manipulated by a state or state-sponsored group. An advanced persistent threat APT is a form of cyberattack in which adversaries infiltrate a target environment and remain undetected for an extended period while systematically collecting or exfiltrating data. These attacks are typically carried out by advanced persistent threat groups, including nation states, organized cybercriminal groups, or highly coordinated apt actors.

The main goal of an advanced persistent threat attack is to gain and maintain long-term, unauthorized access to a target's systems or data without detection.
What makes APTs unique is not just their sophistication, but their persistence. Unlike traditional attacks that aim for immediate disruption, APT campaigns are designed to quietly gain unauthorized access, establish a foothold, and operate within a secure location inside the network for as long as possible. During this time, attackers often focus on high-value assets such as intellectual property, financial records, and other forms of critical business information.
The scale and patience of these attacks are significant. The average dwell time for an APT is approximately 95 days as of 2026, though investigations have shown that some attackers maintained access for years. This persistence is what allows APTs to cause long-term damage while remaining largely invisible to security teams.
History and Evolution of APTs
Advanced persistent threats have been reshaping the cybersecurity landscape for over twenty years, with security researchers first documenting these sophisticated attack campaigns in the early 2000s. Back then, APTs represented the exclusive playground of nation-state actors — well-funded government teams with deep pockets and long-term strategic objectives targeting critical infrastructure and sensitive government networks. The threat landscape looks dramatically different today. Modern APT groups encompass a diverse ecosystem that extends far beyond state-sponsored operations to include organized criminal enterprises and ideologically-driven hacktivist collectives, all wielding advanced persistent tactics to pursue their varied agendas.
What makes today's APT campaigns particularly concerning is their technical sophistication compared to earlier generations of threats. Where first-wave attackers relied primarily on custom malware paired with rudimentary social engineering techniques, contemporary APT groups have assembled formidable arsenals featuring zero-day exploits, precision-crafted spear phishing campaigns, and complex multi-stage attack sequences designed to evade detection. Take Fancy Bear, the group security researchers widely attribute to Russian military intelligence — their operations have become a case study in persistence and stealth, demonstrating an uncanny ability to maintain network access for months or even years without triggering security alerts. As these persistent threats continue evolving their tactics and techniques, security teams face an ongoing arms race against adversaries who combine technical expertise with seemingly unlimited patience and resources.
Characteristics of APT Attacks
The APT Challenge: Why These Attacks Represent Cybersecurity's Most Persistent Threat
Advanced Persistent Threat (APT) attacks have emerged as the cybersecurity equivalent of a master burglar casing a bank for months before striking. These campaigns differ fundamentally from run-of-the-mill cyber incidents. APT operations are typically backed by nation-state actors or well-funded criminal organizations with deep pockets and even deeper patience. They're willing to spend months, sometimes years, pursuing a single target.
Inside the APT Playbook: How Attackers Build Their Arsenal
The hallmark of these threat actors lies in their systematic approach to compromise. Rather than relying on spray-and-pray tactics, APT groups craft bespoke attack tools tailored specifically for their targets. We're talking custom malware that security researchers have never seen before, zero-day vulnerabilities that vendors don't know exist, and lateral movement techniques designed to slip past even advanced detection systems. These aren't script kiddies looking for a quick score — they're digital espionage operations with clear objectives and the technical sophistication to achieve them.
The Long Game: How APTs Maintain Their Foothold
What makes these attacks particularly dangerous is their commitment to staying hidden. APT actors understand that detection means game over, so they've perfected the art of digital invisibility. They'll modify their tools when defenders adapt, establish multiple backdoors across compromised networks, and operate with the kind of operational security that would impress intelligence agencies. This persistence allows them to remain embedded in targeted environments for extended periods — security firm reports regularly uncover APT campaigns that have been active for years before discovery.
The Strategic Stakes: Why APT Attacks Keep CISOs Awake at Night
The ultimate impact of APT campaigns extends far beyond typical data breaches. These operations target the crown jewels of modern organizations: intellectual property that took decades to develop, financial systems that power global commerce, and critical infrastructure that entire economies depend on. When APT groups successfully establish long-term access to these environments, the potential for damage — whether through espionage, sabotage, or large-scale data theft — requires organizations to fundamentally rethink their defensive strategies. Traditional perimeter security simply isn't enough when facing adversaries with this level of resources and determination.
How an APT Attack Works
The lifecycle of an APT typically includes phases such as infiltration, expansion, and extraction. Each phase is designed to deepen access while minimizing detection.
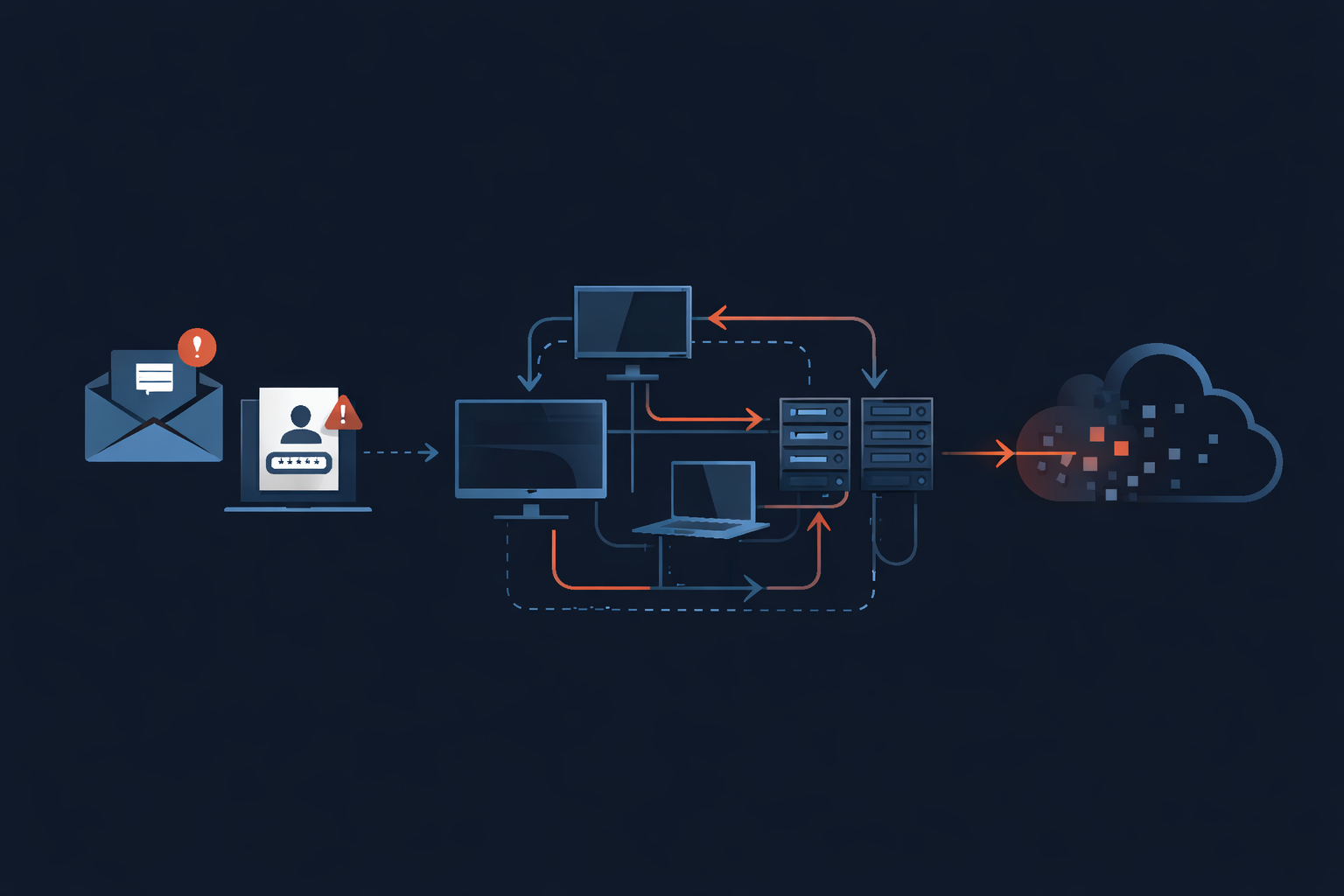
Initial Access and Infiltration
Every advanced persistent threat attack begins with an initial compromise, where attackers attempt to gain initial access to a target network. This phase often relies heavily on social engineering tactics, particularly spear phishing, which remains one of the most effective entry points. In addition to technical methods, APT actors may employ human intelligence techniques — such as traditional espionage and infiltration — to gain access to physical locations or sensitive networks.
APT groups rely on deception as much as technology. Attackers may impersonate trusted contacts, exploit user accounts, or compromise external vendors in supply chain attacks. In many cases, attackers also exploit zero day exploits or vulnerabilities in network software to bypass traditional defenses.
In 2026, nearly 90% of APT investigations involve identity-driven attacks, especially targeting non-human identities such as APIs, service accounts, and automation systems. This shift highlights how attackers are evolving beyond traditional endpoints to exploit identity as the primary attack surface.
APT Attack Vectors
Advanced Persistent Threat campaigns have evolved into highly sophisticated operations that begin with meticulous planning and reconnaissance. These threat actors typically launch their initial assault through carefully orchestrated spear phishing campaigns, crafting convincing emails tailored to specific targets within an organization. The goal is straightforward yet devastating: extract credentials or deliver malicious payloads that grant that crucial first foothold. When social engineering fails, these groups pivot to exploiting unpatched vulnerabilities in network infrastructure — a reminder that outdated software remains one of cybersecurity’s most persistent weak points.
The real danger emerges once attackers establish their beachhead within the target environment. APT groups excel at blending technical sophistication with psychological manipulation, using social engineering to extract additional credentials while simultaneously deploying advanced tools for privilege escalation. Their lateral movement across networks resembles a careful chess game, with each move designed to expand access to high-value systems and sensitive data repositories. These threat actors continuously monitor network communications, adapting their tactics based on defensive responses and ensuring their operations remain under the radar of security teams.
Defending against these persistent adversaries requires a multi-layered approach that goes beyond traditional perimeter security. Organizations need robust detection capabilities through web application firewalls and intrusion detection systems, but technology alone won’t suffice. The most effective defense strategies combine continuous monitoring of the organization's network with aggressive patch management, encryption, and comprehensive employee security awareness programs. Continuous monitoring is essential for proactive threat detection and rapid response to APT activity. Securing the organization's network also requires regular patching, strong encryption practices, and ongoing employee training to reduce the risk of compromise. Success hinges on detecting and neutralizing initial compromise attempts before attackers can establish persistence and begin their methodical advance toward crown jewel assets.
Expansion, Persistence, and Lateral Movement
Once inside the network, APT attackers begin expanding their presence. They establish persistence by deploying malicious files, installing backdoors, and leveraging remote management tools to maintain access even if initial entry points are discovered.
A defining characteristic of APT campaigns is lateral movement. Rather than staying confined to a single compromised system, attackers move across the network, escalating privileges and accessing additional systems. This often involves exploiting weak access control policies, reusing credentials, or hijacking legitimate sessions such as a user’s SSH connection. Attackers may use tactics such as DDoS attacks to distract network personnel while conducting malicious activities.
During this phase, attackers frequently communicate with command and control servers, which act as external hubs for managing compromised systems. These servers allow APT actors to issue commands, exfiltrate data, and coordinate ongoing operations while remaining hidden within normal network traffic. APT actors often use malware to explore the network and exfiltrate data without detection.
The objective is clear: maintain access, deepen control, and ensure the attack remains undetected for as long as possible.
Command and Control Servers
Command and control servers represent the beating heart of today’s most sophisticated cyber campaigns, providing threat actors with the remote access they need to orchestrate complex, multi-stage attacks against enterprise networks. Whether deployed on compromised cloud infrastructure or cleverly embedded within a victim’s own systems, these C2 nodes function as digital command centers where attackers coordinate malware distribution, execute reconnaissance, and systematically extract valuable data from their targets.
Modern APT campaigns demonstrate remarkable ingenuity in how they maintain communication with these control servers. Security researchers have documented cases where threat groups embed C2 traffic within seemingly benign HTTPS connections, disguise command channels as routine DNS queries, or even leverage popular social media platforms as covert communication hubs. These techniques create a detection nightmare for network defenders, who must differentiate between legitimate business traffic and carefully crafted attack communications flowing through the same channels.
The challenge for security teams lies in building detection capabilities that can identify these stealthy connections before attackers achieve their objectives. Organizations that invest in behavioral network monitoring, implement strict egress filtering, and deploy threat hunting programs consistently outperform those relying solely on signature-based defenses. The most effective approaches combine automated anomaly detection with human expertise, enabling security analysts to spot the subtle indicators that reveal when systems have been compromised and are communicating with external controllers. Security personnel play a crucial role in actively monitoring and responding to unusual network activities, such as irregular logins or data transfers, which is essential for detecting and mitigating advanced persistent threat communications.
Data Extraction and Stealth Operations
The final stage of an APT attack focuses on data extraction. By this point, attackers have mapped the network, identified valuable assets, and positioned themselves to quietly steal sensitive data.
Data exfiltration is often performed gradually to avoid detection. Attackers may disguise outbound data as legitimate traffic or route it through encrypted channels to an external server. This allows them to extract large volumes of information — including intellectual property, financial records, and sensitive operational data — without triggering alarms.
Because APT operations are designed to remain hidden, many organizations only discover the breach months later, often after significant damage has already occurred.
Cyber Espionage and APT Activities
Cyber espionage operations represent the core mission driving most Advanced Persistent Threat campaigns today. APT groups systematically pursue high-value targets — intellectual property, financial records, and mission-critical business intelligence — that can deliver substantial strategic or economic leverage. These groups use cyber techniques to gather intelligence on governments, companies, and other entities over extended periods. These campaigns typically trace back to nation-state actors or well-funded criminal organizations equipped with the resources and patience necessary for long-term intelligence gathering operations.
The attack methodologies deployed by APT actors span an increasingly sophisticated spectrum of techniques designed to penetrate organizational defenses and extract sensitive data. Social engineering remains a cornerstone tactic, often combined with network exploitation techniques and advanced database manipulation to access protected information stores. Security researchers have documented APT presence across virtually every major industry sector, from government agencies to financial institutions and technology companies, illustrating just how pervasive these persistent threat actors have become in the modern threat landscape.
Beyond conventional direct-attack vectors, APT groups have refined their approach to include supply chain compromises and advanced stealth operations that can evade detection for months or even years. These attackers strategically target trusted third-party vendors or exploit previously unknown vulnerabilities to circumvent established security controls, establishing persistent footholds within victim networks. The continuous evolution of cyber espionage tactics demands that organizations adopt equally sophisticated defensive strategies, investing in advanced threat detection capabilities and comprehensive security frameworks designed to protect critical assets against increasingly determined and well-resourced adversaries.
Real-World Examples of Advanced Persistent Threat Attacks
APT attacks have had profound impacts on global cybersecurity. One of the most well-known examples is the Stuxnet worm, which targeted Iran’s nuclear program and demonstrated how cyber operations could disrupt physical infrastructure.
Groups such as Fancy Bear, linked to russian military intelligence, have conducted widespread cyber espionage campaigns targeting governments, corporations, and critical infrastructure. These advanced persistent threat groups operate with precision and strategic intent, often aligning with geopolitical objectives. The widespread presence of APTs within critical infrastructure, government agencies, and organizations with valuable data underscores their significant and ongoing footprint across various sectors and regions.
Research from Mandiant in 2013 revealed that APT campaigns lasted an average of one year, with some attackers maintaining access for nearly five years. More recently, a major healthcare organization experienced a breach in February 2024 that impacted approximately 190 million individuals — highlighting the continued scale and impact of APT threats.
Why APT Threats Are So Dangerous
APT threats pose a unique challenge because they combine stealth, persistence, and sophistication. Unlike traditional attacks that trigger immediate alerts, APT campaigns are designed to blend into normal operations and remain undetected.
These attacks often target critical systems and sensitive systems, including those tied to critical infrastructure. The consequences can include large-scale data theft, long-term espionage, and even operational disruption.
Organizations that store large volumes of personally identifiable information or proprietary data are especially vulnerable. For these organizations, a successful apt attack can result in financial loss, reputational damage, and regulatory consequences. Implementing robust security measures is essential to protect organizations from advanced persistent threats and mitigate cyber risks.
Detecting APT Activities
Detecting apt activities requires a shift from reactive security to proactive monitoring. Because APT attackers use advanced techniques and sophisticated tools, traditional defenses alone are often insufficient.
Security teams must focus on identifying subtle indicators, such as:
- Unusual network traffic
- Unexpected remote connections
- Anomalies in database operations
These signals may indicate that attackers are operating within the network.
This is where threat intelligence and threat hunting become critical. By continuously analyzing data and looking for patterns, organizations can identify APT threats earlier in their lifecycle. Advanced security solutions, including AI and machine learning, further enhance detection by identifying behaviors that deviate from normal activity. AI and machine learning are particularly effective at detecting sophisticated threats that traditional security measures may miss.
Preventing Advanced Persistent Threat Attacks
Preventing an advanced persistent threat requires a comprehensive, layered approach that addresses both technology and human risk. Key prevention strategies include:
- Strong access control:
- Enforce least privilege access
- Require multi-factor authentication
- Limit lateral movement and privilege escalation
- Monitor ingress and egress traffic:
- Detect installation of backdoors
- Identify exfiltration of stolen data
- Analyze traffic entering and leaving the network for suspicious activity
- Whitelisting:
- Designate a specific set of trusted applications and domains
- Minimize attack surfaces and limit tools available to attackers
- Deploy advanced technologies:
- Use AI and machine learning to analyze data and identify APT behavior
- Combine with threat intelligence for early detection
- Invest in advanced security technologies as a long-term strategy
- Deploy security tools:
- Use web application firewalls (WAF) to filter incoming traffic and protect web application servers from application layer attacks (e.g., RFI, SQL injection)
- Employee awareness:
- Conduct regular security training
- Teach employees to recognize phishing attempts and suspicious activity
- Incident response planning:
- Prepare to quickly contain and eradicate threats once detected
- Regularly test and update incident response plans
Protecting the organization's network requires both proactive and reactive cybersecurity measures to safeguard digital infrastructure from advanced threats.
Incident Response Planning for APTs
Advanced persistent threat attacks continue to pose one of the most significant challenges facing enterprise security teams today. The sophisticated nature of these campaigns allows threat actors to maintain undetected access to corporate networks for months or even years, systematically exfiltrating sensitive data while avoiding traditional detection mechanisms. Organizations that fail to implement comprehensive incident response frameworks often discover breaches only after substantial damage has already occurred, making rapid detection and containment capabilities absolutely critical for modern cybersecurity operations.
Building an effective incident response strategy extends far beyond deploying the latest security technologies. While advanced threat hunting tools and real-time intelligence feeds form the technical foundation, successful programs require well-defined operational procedures, including:
- System isolation protocols: Quickly isolate affected systems to prevent further spread.
- Data recovery processes: Restore compromised data from secure backups.
- Stakeholder communication workflows: Ensure timely and accurate communication with internal and external stakeholders.
- Regular security assessments: Continuously evaluate and improve security posture.
- Continuous network monitoring: Maintain visibility to identify potential attack vectors before they're weaponized.
These proactive measures enable security teams to spot anomalous behavior patterns that often signal the early stages of persistent threat campaigns.
The most resilient organizations approach APT prevention through layered defensive strategies that combine technical controls with human expertise, such as:
- Robust access management frameworks
- Strategic network segmentation
- Comprehensive security policy enforcement
However, technology alone cannot counter determined adversaries. Investment in specialized training programs that teach security professionals to recognize subtle indicators of compromise and execute decisive response protocols ultimately determines whether an organization can neutralize persistent threats before they achieve their objectives.
Key Takeaways for Security Teams
Advanced persistent threats represent a long-term, evolving risk that cannot be addressed with a single solution. Organizations must adopt a proactive, layered defense strategy that combines:
- Identity security
- Network monitoring
- Advanced detection technologies
- Employee awareness
By investing in advanced security technologies, strengthening security policies, and maintaining continuous visibility across their environments, organizations can significantly improve their ability to prevent apt attacks and respond effectively when they occur.
FAQ: Advanced Persistent Threat (APT)
What is an advanced persistent threat?
An advanced persistent threat is a long-term cyberattack where attackers infiltrate a network and remain undetected while stealing sensitive data.
What makes an APT attack different?
APT attacks are persistent, highly targeted, and designed to operate stealthily over months or years rather than causing immediate disruption.
Who carries out APT attacks?
APT attacks are typically conducted by nation states, organized cybercriminal groups, or highly skilled threat actors with significant resources.
How do APT attackers gain access?
They commonly use spear phishing, exploit vulnerabilities, and leverage social engineering tactics to gain initial access.
What is lateral movement in APT attacks?
It is the process of moving across systems within a network to expand access and reach sensitive data.
How can organizations prevent APT attacks?
By implementing strong access control, monitoring network traffic, using threat intelligence, training employees, and deploying advanced security solutions.
Why are APT threats so difficult to detect?
Because they are designed to blend into normal network activity and remain undetected for extended periods.